How To: Connect to a remote mysql server using mysqlcc and ssh tunneling part 2
In a previous article we saw how to connect to a remote mysql server running both ssh and mysql.
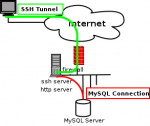
This time, we are going a bit further and will see howto connect to a remote server running ssh in order to be able to access a sql server on the remote LAN.
This system allow to hide the SQL server from the outside. Please, keep in mind that in this example, we are connecting to a MySQL server, but it could be any service running there.
Let’s put it on the table. Imagine that we have got a web server which is put under high load, a clever way to soften the effect of the load and in the same way protect our SQL datas from the outside will be to have the HTTP server available to the outside (so it can serve the web pages), and hide our MySQL server from the outside.
This will look like this:
We saw last time, that in order to securely connect to a remote MySQL server running both mysql and ssh, we had to create a tunnel between our desktop and the server where we had to forward port 3307 on our desktop to port 3306 running locally on the remote server by giving the following intruction to ~/.ssh/config:
Localforward 3307 localhost:3306
This time, we want to forward port 3307 on our desktop to port 3306 on the MySQL server (let says it as 192.168.0.3 as IP adress). The only change we have to make to the previous configuration is to change the Localforward instruction by:
Localforward 3307 192.168.0.3:3306
And simply use the same mysqlcc configuration as the one given in the How To Connect to a remote mysql server using mysqlcc and ssh tunneling Tutorial. It is as simple as that :). Here is an overview of the final configuration we have deployed:
People which do not want to use ~/.ssh/config might use the following command:
tester@laptop:~$ ssh -L 3307:192.168.0.3:3306 [email protected]
Now, you can play around with port forwarding, later on, I will show you how to go even further and just do some useless be geeky thing.
cheerio